Big data and visual analytics brought groundbreaking new capabilities to intelligence systems, allowing improved analytics and sense making on large amounts of data from many sources – especially when coupled with support for data integration between different databases, collaboration between analysts and information exchange between organizations.
ObjectSecurity is part of the unique multi-year project “VALCRI”, which is concerned with visual analytics for police intelligence. As part of the project, ObjectSecurity has developed an innovative security architecture for such demanding tasks based on its innovative OpenPMF security policy automation platform. OpenPMF allows the intuitive authoring of rich, but human-understandable policies driven by operational and regulatory security and data protection requirements. From these policies, OpenPMF automatically generates the matching technical security enforcement for “defense in depth” across many systems and technology layers.
Access to data is a risky business.
Access to data and processed intelligence also brings risks, in some cases so many risks that they prohibit the full use of the new systems. Access to information has to be contextually restricted to the minimum necessary for analysts to do their current tasks. Not all users, including analysts, are authorized to access all data in the systems – they may not have sufficient clearance, or there is no need to know, or because data has to be specifically protected.
Other data may only be obtained under specific conditions and is bound to a specific purpose. In some countries and domains, for example in police intelligence, strict data protection regulations have to be met. Meeting those using conventional security technologies is not only challenging, it is almost impossible, as history has shown. Security and audit requirements. In addition, the usage of the system has to be strictly audited, including system administrators – to detect misuse by insiders and attacks from the outside.
About VALCRI.
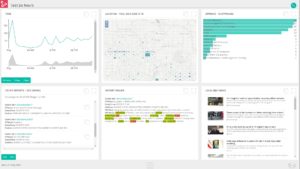
At the cutting edge of intelligence-led policing, VALCRI is a semi-automated analysis system that helps find connections humans often miss. When pre-empting crime or investigating a case, it can be deployed by analysts to reconstruct situations, generate insights and discover leads.
Through autonomous work or collaboration with a human team, VALCRI creatively analyses data from a wide range of mixed-format sources. It displays its findings with easy-to-digest visualisations, comes up with possible explanations of crimes, and paves the way for rigorous arguments. Protecting against human error and bias, VALCRI works with objective intelligence, speed and precision.
About OpenPMF Security Policy Automation.
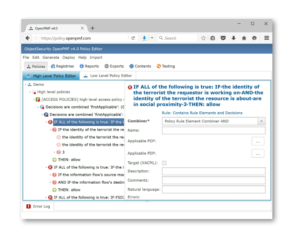
OpenPMF Security Policy Automation and Management Platform from ObjectSecurity stops security breaches and data leakage with powerful policy enforcement, and makes security policy manageable through automation. OpenPMF is the “umbrella” platform for security policy management.
OpenPMF allows organizations to implement rich policies with consistency – organization-wide “in depth” across many technologies and layers. OpenPMF lets you do this in a way that is easy to implement, manage and audit. You can author and maintain powerful yet intuitive security policies across your IT landscape, including for example Attribute Based Access Control (ABAC).